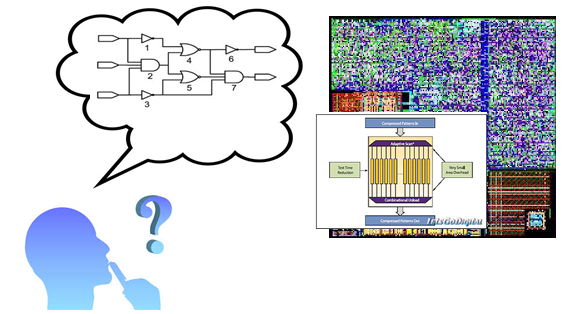
The goal of this project is to provide the students with a deep knowledge, understanding and experience of all stages of the VLSI design process from concept to the testing of the fabricated silicon. In this project, the students will design and implement a hardware accelerator for an image demosaic algorithm.